In the volatile realm of Web3, where digital assets represent hard-earned wealth, the fragility of traditional seed phrases has long undermined user confidence. A single misplaced 12- or 24-word sequence can spell irreversible loss, exposing investors to phishing scams, hardware failures, or simple human error. Enter seedless wallet recovery mechanisms powered by WebAuthn smart wallets. These innovations, rooted in passkey technology, promise phishing-resistant authentication and multi-layered safeguards without the burden of memorizing cryptic phrases. As a seasoned asset manager, I approach these developments with measured optimism: they address real pain points but demand rigorous scrutiny to ensure they truly preserve capital over the long term.
WebAuthn, the cornerstone of modern passkeys, leverages public-key cryptography bound to a user's device secure enclave. Private keys never leave the hardware, authenticated via biometrics or PINs. This shift eliminates seed phrase vulnerabilities while enabling sophisticated recovery models tailored for Web3 users. Yet, convenience must not eclipse caution; each mechanism carries trade-offs in centralization risks or dependency on third-party services.
Cross-Device Passkey Synchronization: Sync Without Sacrifice
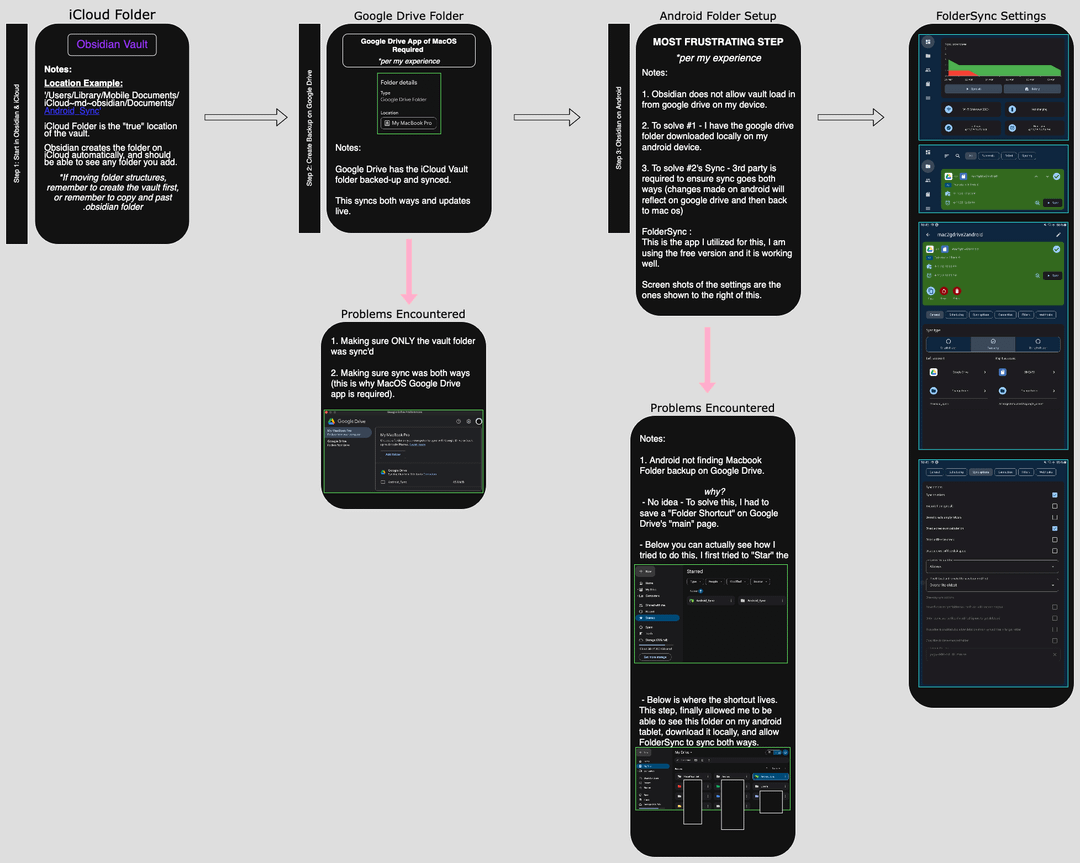
The foundation of WebAuthn passkey recovery lies in cross-device synchronization, where passkeys propagate securely across a user's ecosystem via platform vaults like iCloud Keychain or Google Password Manager. Imagine losing your primary phone: your new device simply prompts biometric approval to inherit the synced credential, restoring wallet access instantaneously. This model shines in everyday scenarios, supporting multi-device workflows essential for developers and power users juggling laptops, tablets, and mobiles.
Analytically, the appeal is clear. Platform providers encrypt passkeys end-to-end, thwarting interception during sync. Adoption metrics from sources like Medium's Bhagya Rana highlight how Apple and Google vaults have matured into reliable conduits, reducing single-device failure rates dramatically. Cautiously, however, users must weigh vendor lock-in; what if policy changes revoke sync privileges? Diversification across platforms mitigates this, echoing timeless investment principles.
Social Guardian Recovery: Leveraging Trusted Networks
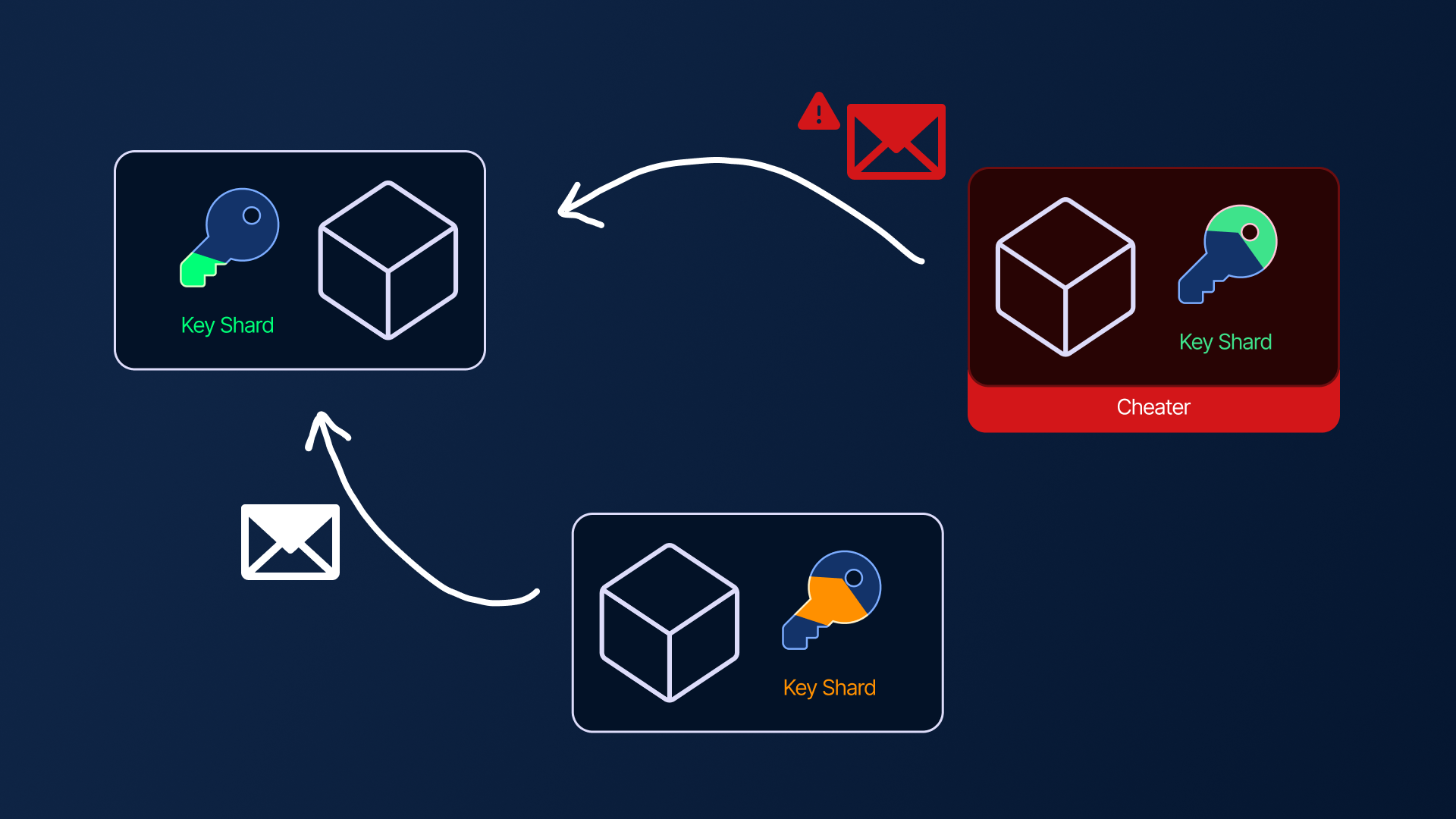
Building on synchronization, social guardian recovery introduces human elements into the equation. Users pre-designate trusted contacts;family members, colleagues, or advisors;as guardians. Upon access loss, a quorum approves recovery via their own passkeys or devices, triggering smart contract logic to regenerate wallet control. Projects like those from SevenX Ventures and Digitap app exemplify this, blending social trust with cryptographic rigor.
This approach humanizes Web3 security, fostering community-backed resilience. In practice, it outperforms solo seed reliance by distributing risk, much like diversified bond ladders in fixed income portfolios. Opinionated take: it's ingenious for non-technical users, but select guardians judiciously; compromised contacts could cascade failures. Threshold quorums;typically 2-of-3 or 3-of-5;add layers, ensuring no single point dominates.
5 Seedless Recovery Models
- Cross-Device Passkey Synchronization: Syncs passkeys across devices using platform vaults like iCloud Keychain or Google Password Manager. Enables multi-device access but depends on vendor security and sync reliability.
- Social Guardian Recovery: Designate trusted guardians; a quorum approves wallet rotation or restoration via smart contracts. Leverages social trust analytically, yet requires careful guardian selection to mitigate coercion risks.

- MPC Shard Recovery via Trusted Channels: Splits private key into shares using MPC or Shamir's Secret Sharing, reconstructed via secure channels. Cautiously reduces single-point failures but demands robust share distribution.
- Secure Enclave Hardware Backup: Stores keys in device secure enclaves (e.g., Apple Secure Enclave) with biometric access. Enhances phishing resistance, though physical device loss poses recovery challenges.
- Threshold Passkey Multi-Authenticator Recovery: Requires threshold of multiple authenticators (devices/biometrics) for recovery. Provides redundancy but introduces complexity in managing multiple points.

Real-world implementations, such as guardian rotations on Binance-inspired protocols, demonstrate efficacy. A cautious lens reveals edge cases: geographic dispersion or guardian unavailability could delay recovery. Nonetheless, when paired with time-locks, it fortifies no seed phrase recovery Web3 strategies effectively.
MPC Shard Recovery via Trusted Channels: Distributed Key Mastery
Multi-Party Computation (MPC) elevates seedless paradigms through shard recovery. Here, the wallet's master key shatters into encrypted fragments, dispersed across devices, emails, or secure servers. Recovery demands recombining shards over trusted channels, sans full key reconstruction. The Block's insights into MPC versatility;spanning phone numbers to passwords;underscore its adaptability for Web3.
From an analytical standpoint, MPC minimizes exposure: even if one shard leaks, the asset remains safe. Threshold schemes, akin to Shamir's Secret Sharing, require only a subset for action, ideal for fragmented user lifestyles. I've long advocated capital preservation; this mirrors it by avoiding single-key cataclysms. Pitfalls persist, though: channel security is paramount, and latency in shard collection could frustrate urgent transactions.
Gate. com's zkSync deployments illustrate MPC in action, with user-cancellable processes adding control. For conservative Web3 adopters, this model's auditability via smart contracts provides reassurance, though quantum threats loom on the horizon, necessitating post-quantum upgrades.
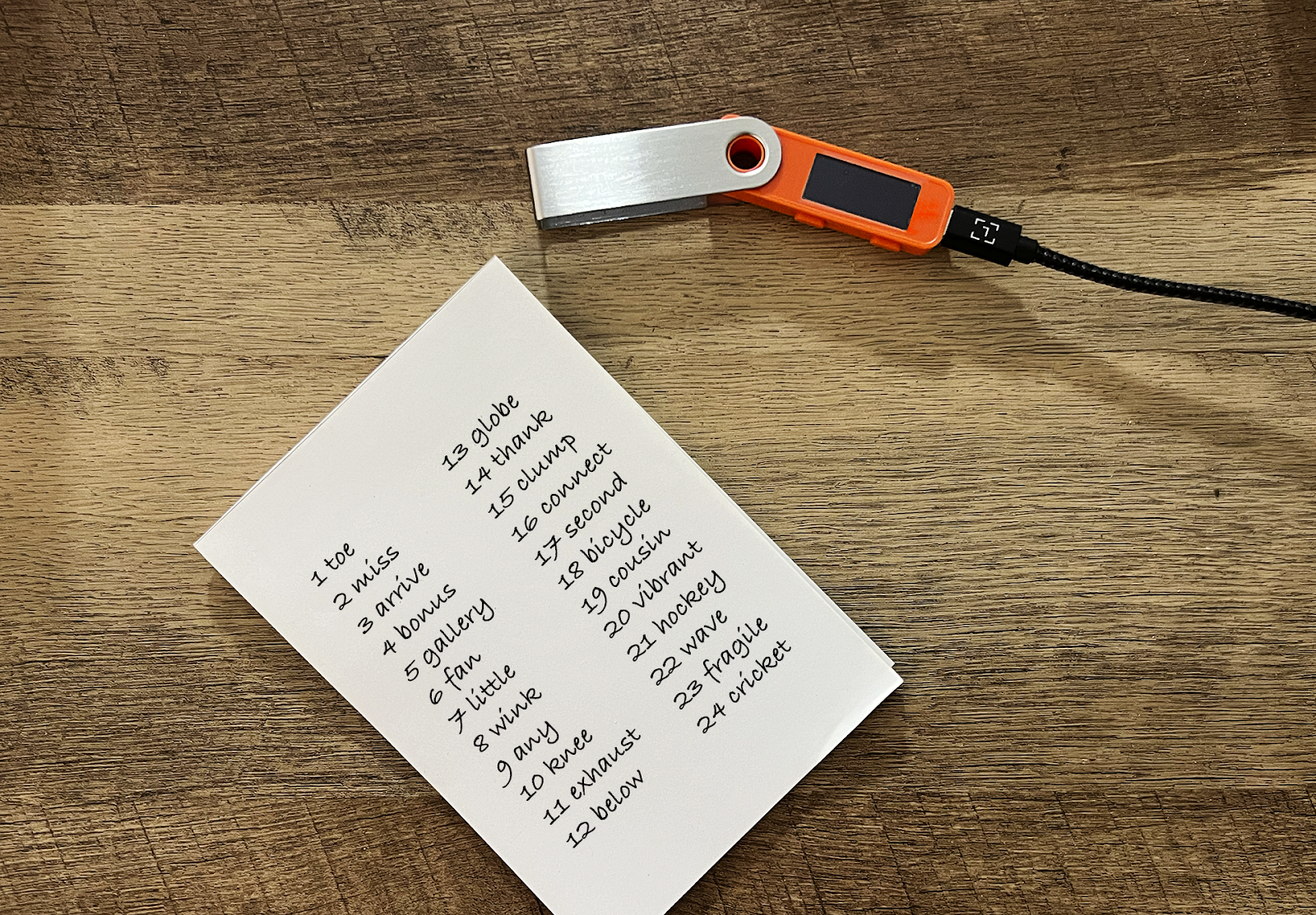
Transitioning to hardware-centric safeguards, secure enclave hardware backup anchors recovery in the unbreachable fortresses of modern devices. Apple's Secure Enclave or equivalents like Qualcomm's Secure Processing Unit store passkey derivatives immutably, shielded from OS-level exploits. Backup involves exporting encrypted blobs to trusted secondary hardware, retrievable only via original biometrics. This method, echoed in Hacker News discussions on Ledger integrations, appeals to those prioritizing offline resilience over cloud dependency.
Secure Enclave Hardware Backup: Fortress-Level Fortification
Analytically dissecting this model reveals its prowess in phishing resistance: enclave operations demand physical possession and biometric verification, rendering remote attacks futile. For Web3 users managing substantial holdings, it's a conservative bulwark, preserving capital akin to gold vaults in traditional finance. Cautiously, hardware obsolescence poses risks; what happens when Secure Enclave tech evolves incompatibly? Proactive exports to Ledger-style hardware wallets bridge this, transforming ephemeral device keys into enduring backups without seed phrases.
Team1. blog's Avalanche implementations showcase biometrics plus guardians for enclave recovery, blending hardware purity with social layers. In my view, this excels for high-net-worth individuals, but demands discipline in managing multiple hardware nodes, lest one failure cascade.
Comparison of 5 Seedless Recovery Models in WebAuthn Smart Wallets
| Recovery Model | Pros | Cons | Security Level | Usability Score |
|---|---|---|---|---|
| Cross-Device Passkey Synchronization | Seamless sync via platform vaults (iCloud/Google), Phishing-resistant WebAuthn, Multi-device access without seeds | Vendor lock-in to ecosystems, Platform compromise risks, Limited offline recovery | High | 9/10 |
| Social Guardian Recovery | Uses trusted guardians for quorum recovery, No single secret needed, Flexible social trust model | Guardian coordination delays, Social engineering risks, Privacy exposure to contacts | Medium-High | 7/10 |
| MPC Shard Recovery via Trusted Channels | Key shares distributed across devices/servers, Threshold reconstruction, Mitigates single-point failures | Complex setup and channels, Potential latency in recovery, Implementation overhead | Very High | 6/10 |
| Secure Enclave Hardware Backup | Hardware-secured keys with biometrics, Local fast auth, Strong physical protection | Device loss vulnerability, Platform-specific (e.g., Apple), Physical hack risks | Very High | 8/10 |
| Threshold Passkey Multi-Authenticator Recovery | Multiple passkeys for threshold auth, ERC-4337 integration, Customizable security | Multi-device dependency, Sync management needed, Higher user setup effort | High | 7/10 |
Threshold Passkey Multi-Authenticator Recovery: Collective Consensus for Control
Crowning these innovations, threshold passkey multi-authenticator recovery mandates approval from multiple registered authenticators - say, two phones and a laptop - to initiate recovery. Leveraging WebAuthn's multi-credential support, it enforces distributed consent, preventing unilateral device dominance. YouTube explorations by James Bachini on Stellar smart wallets hint at this via SOR band contracts, where passkeys orchestrate threshold signatures.
This mechanism's analytical edge lies in redundancy: lose one device, no sweat; adversaries need to compromise several. It embodies diversification, my mantra for sustainable wealth, scattering risk across authenticators while upholding passkey smart wallet backup standards. Cautions abound, however: coordinating approvals during crises tests user preparedness, and sync discrepancies could lock funds temporarily. TeleSwap's emphasis on WebAuthn phishing defenses bolsters its case, positioning it as a mature choice for daily crypto management.
Synthesizing these five pillars - cross-device synchronization, social guardians, MPC shards, secure enclaves, and threshold multi-auth - unveils a robust ecosystem for WebAuthn multi-device sync and beyond. Each tailors to user profiles: sync for nomads, guardians for families, MPC for tech-savvy, enclaves for purists, thresholds for enterprises.
Yet scrutiny reveals common threads of caution. Vendor ecosystems, while polished, invite centralization whispers; Apple's dominion over iCloud vaults mirrors big tech's sway in finance. Smart contract audits remain non-negotiable, as zkSync cases from Gate. com affirm, with 48-hour cancellation windows as prudent delays. Quantum shadows, per eprint. iacr. org protocols, urge ongoing evolution toward post-quantum primitives.
For Web3 pioneers weary of seed phrase roulette, these mechanisms herald a paradigm shift, marrying convenience with capital preservation. Patience, as in dividend growth strategies, rewards those vetting implementations rigorously. Diversify recovery vectors, monitor platform shifts, and these tools could underpin the next decade of decentralized asset stewardship, stress-testing WebAuthn's promise against real-world volatility.





No comments yet. Be the first to share your thoughts!