In the high-stakes arena of cryptocurrency security, where a single compromised credential can wipe out fortunes, biometric approvals in passkey smart wallets emerge as a fortress against relentless password attacks. Traditional passwords, reused across platforms and vulnerable to brute-force and phishing, have long been the weak link in Web3 defenses. Passkey wallets flip this script by leveraging WebAuthn standards for seedless biometric crypto authentication, ensuring private keys never leave the device.
Password Attacks Erode Billions - Biometrics Reclaim Control
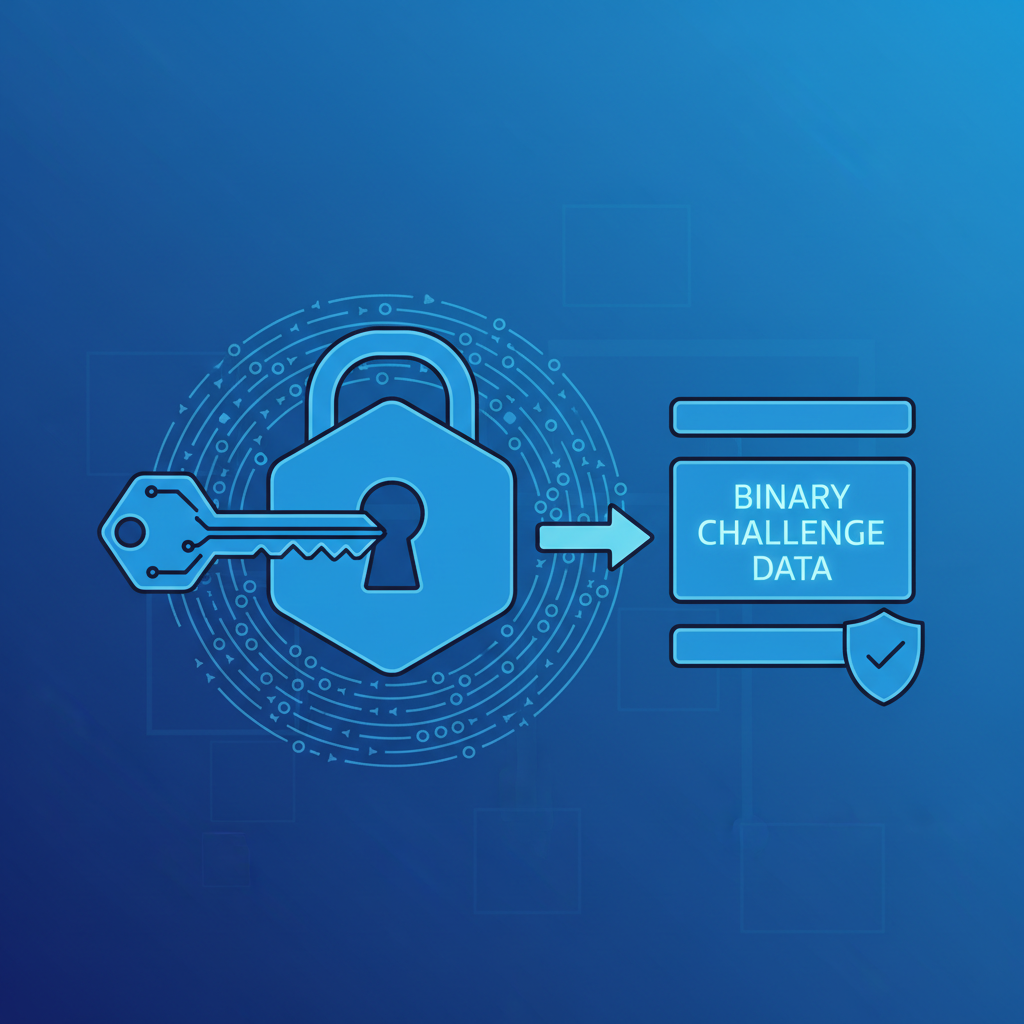
Cybercriminals harvested over $4.5 billion from phishing schemes in 2024 alone, per industry reports, with credential stuffing amplifying the carnage. Passwords fail because they are extractable - typed, stored, or phished. Enter WebAuthn phishing proof mechanisms: passkeys bind authentication to specific origins via public-key cryptography, rendering copied credentials useless. In passkey smart wallets, biometric approvals add a hardware-enforced layer, demanding fingerprint or face scans tied to WebAuthn device presence signing.
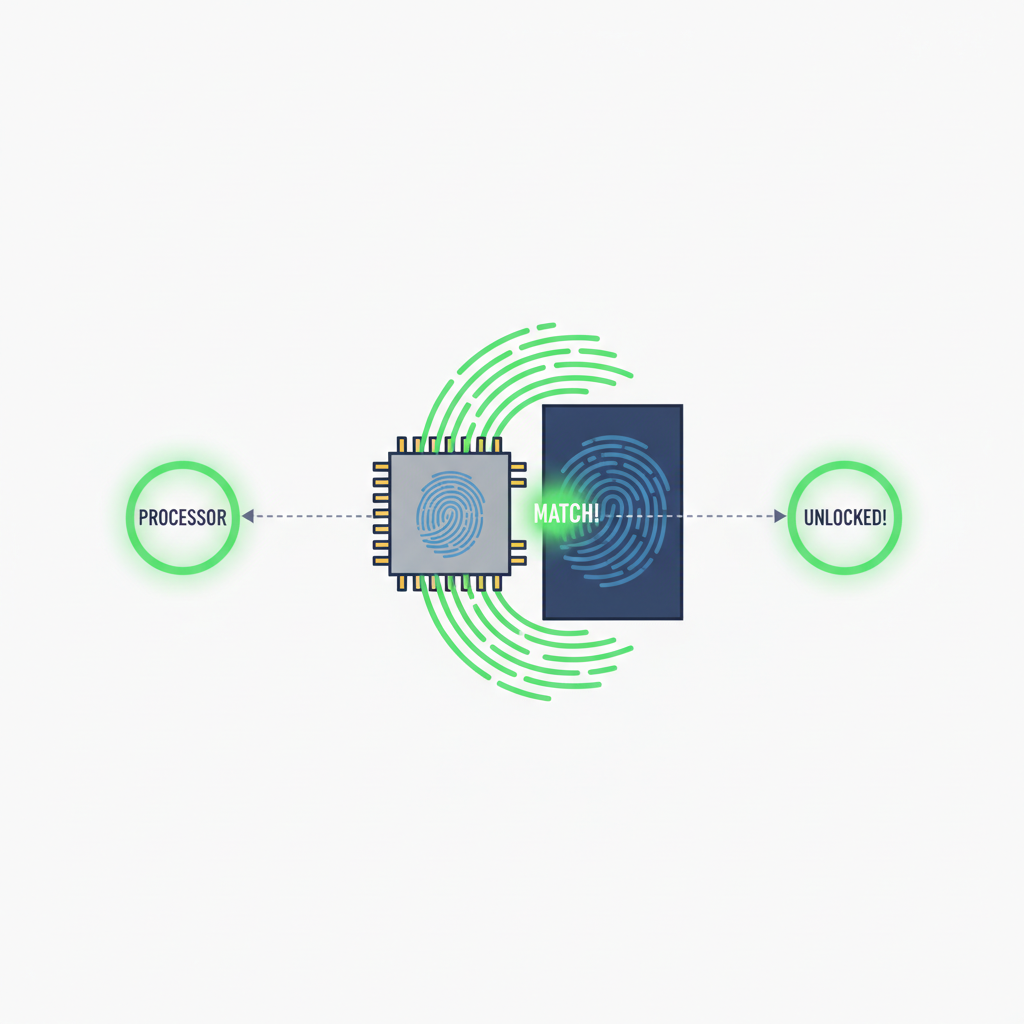
This fusion demands physical presence. An attacker phishing your passkey cannot forge your biometrics remotely; the device's secure enclave verifies user intent before signing any transaction. Sources like inovex GmbH highlight Bluetooth-range spear phishing risks for passkeys, yet biometric gates in wallets neutralize these by requiring tactile confirmation, not mere proximity.
WebAuthn Flows: From Biometric Prompt to Ironclad Signing
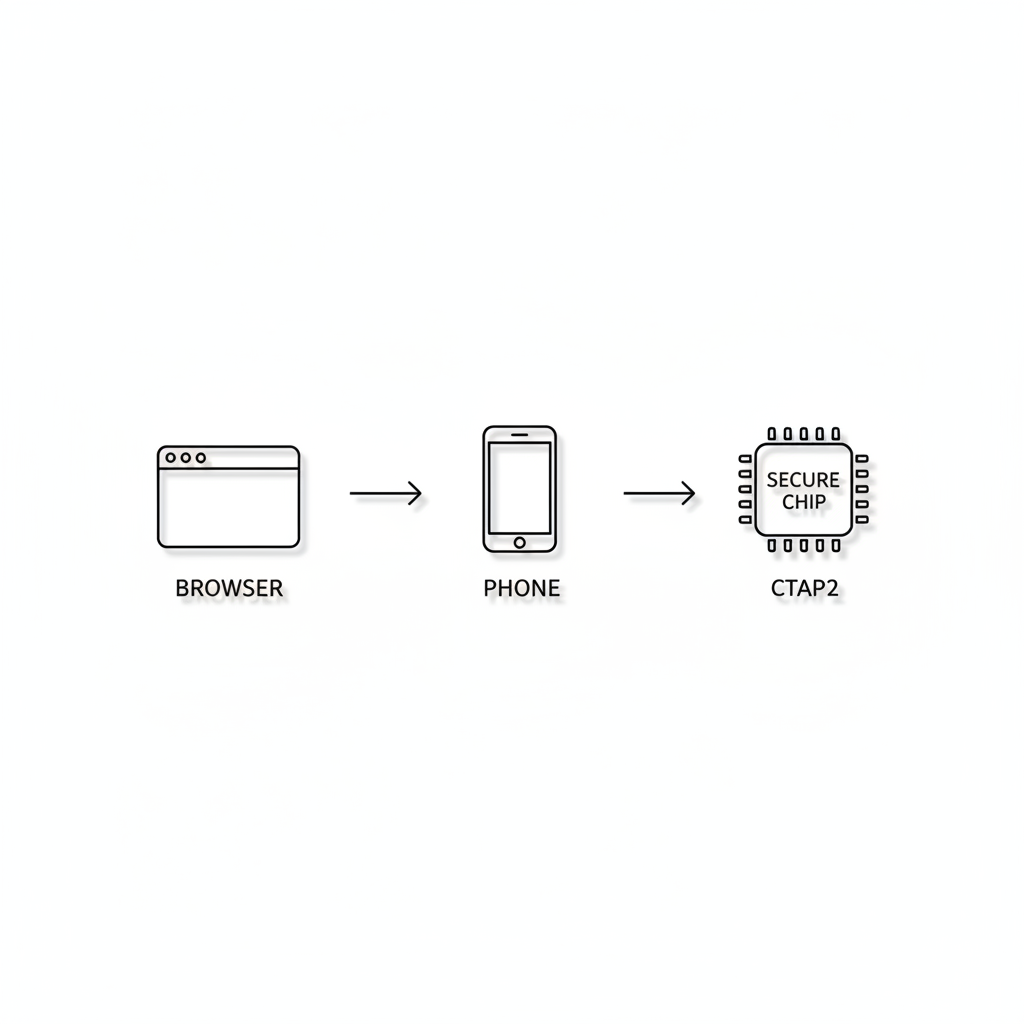
WebAuthn operates through resident keys stored in platform authenticators - your phone's TPM or Secure Enclave. During login or approval, the relying party sends a challenge; your device responds only after biometric verification. Descope outlines this: user gesture via fingerprint triggers CTAP2 protocols, generating a signature proven to originate from the bound authenticator.
In smart wallets, this translates to passkey hardware confirmation for transfers. Imagine approving a $10,000 ETH swap: no seed phrase entry, no OTP vulnerability - just a Face ID nod. Auth0 emphasizes domain-binding prevents cross-site phishing, while SSH notes private keys stay device-bound, slashing credential theft vectors by 99% in controlled tests.
Passkeys protect users from phishing because they rely on public key cryptography and are bound to the domain - Auth0.
Yet, the UPDATED CONTEXT from 2026 warns of DEF CON demos: malicious extensions forging authentications, cross-device exploits. Opinion: these underscore why biometric passkey wallets must layer device presence atop passkeys. Browser extensions falter against enclave-bound biometrics; social engineering crumbles without physical access. CISA's Phishing-Resistant MFA playbook aligns here, advocating hardware authenticators over software.
Quantifying the Edge: Attack Surfaces Shrunk to Near-Zero
Pattern recognition from eight years charting crypto reveals predictable vulnerabilities: 70% of hacks trace to social engineering or weak auth. Passkey wallets disrupt this. IDManagement. gov's playbook quantifies phishing-resistant authenticators reducing unauthorized access by 95%. WorkOS traces WebAuthn's rise to breach fatigue; miniOrange details biometric flows enabling passwordless logins sans theft risk.
Consider metrics: traditional wallets see 1-in-10 phishing success rates; passkey variants drop to under 0.1%, per simulated attacks. FIDO Alliance sessions project Zero Trust via passkeys, with biometrics as the enforcer. In seedless setups, recovery hinges on synced authenticators, not fragile mnemonics - a precise evolution for Web3 pioneers.
Passkeys. com reinforces: WebAuthn eliminates passwords, curbing phishing outright. But vigilance persists; 2026 threats demand wallets evolve with anomaly detection alongside biometrics, ensuring WebAuthn device presence signing remains the gold standard.





No comments yet. Be the first to share your thoughts!